AWS IoT Greengrass - Secrets
Welcome to the AWS IoT Greengrass - Secrets brick. In this overview we'll go through setting up Secrets at the edge with AWS IoT Greengrass. The specific parts that we will cover can be seen below:
- Create a Greengrass Secret
- Greengrass Lambda function - Access Secrets
- Create Subscriptions
- Deploy and Test Secret Access
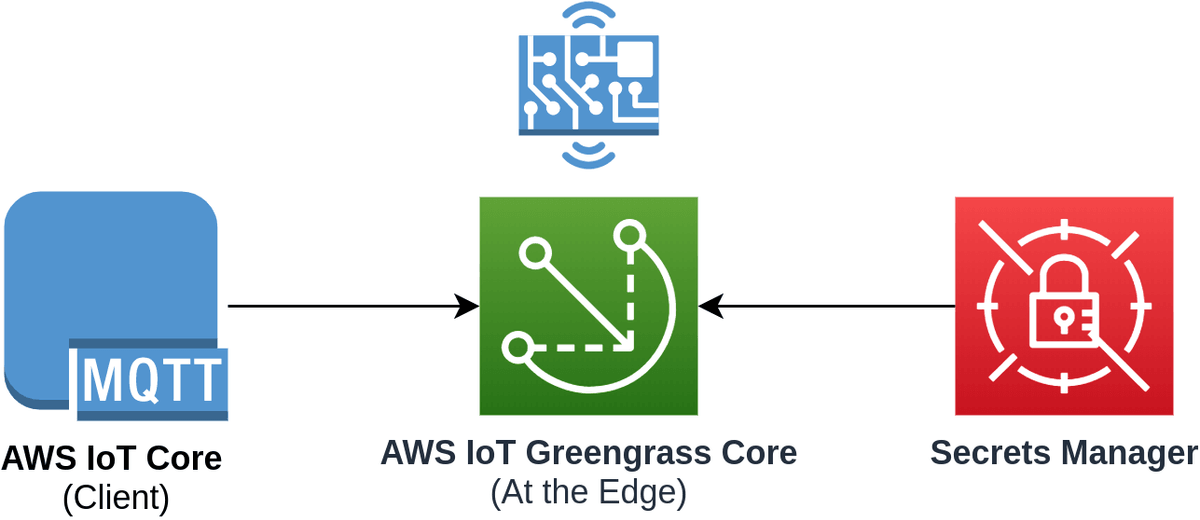
The overall goal of this guide is to demonstrate very simply the following workflow:
Prerequisites
- AWS Account (Free Tier is acceptable)
- existing Greengrass Group & Device - You will need a device with Greengrass Core deployed on it. You can follow one of our previous guides for this:
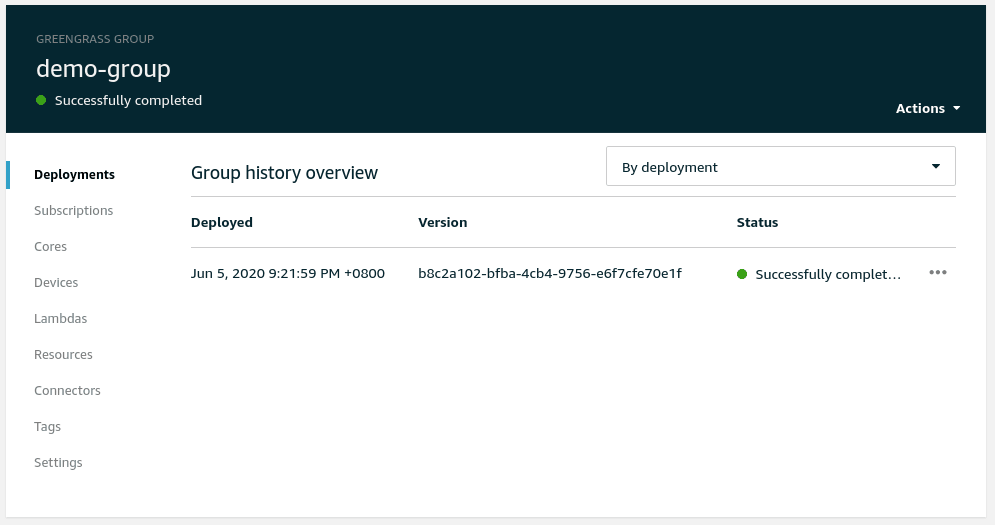
Here is an example of a deployed Greengrass Core setup with minimal configuration that we will be using in this guide
Create a Greengrass Secret
Let's begin by creating a simple secret that will be available at the edge. This could be a Database password or some secret material that we don't want to store in code, but want access to when our IoT device is installed.
Navigate to the AWS IoT Greengrass group that should already be created and click Add a secret resource under the Resources > Secret section.
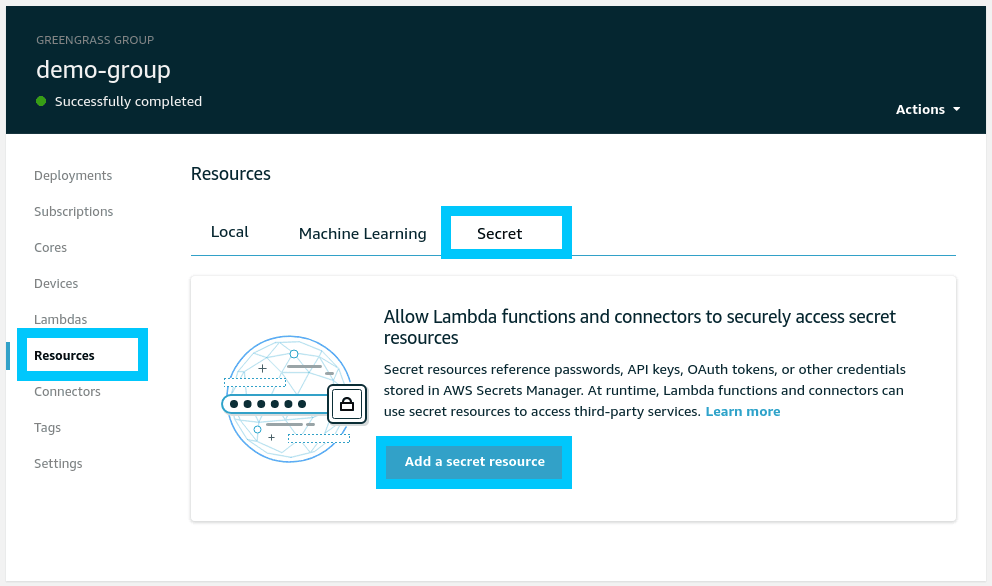
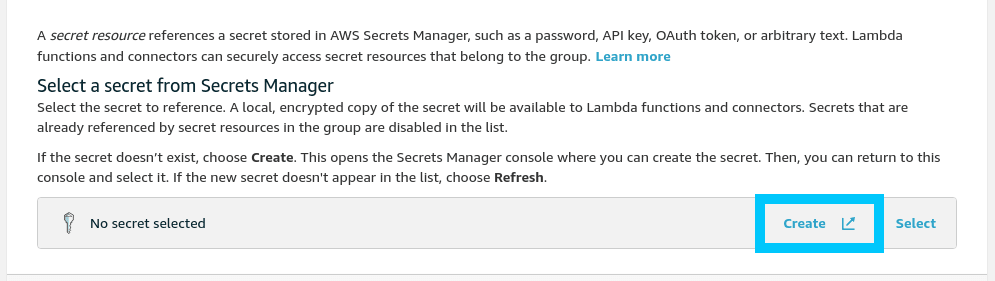
You will be presented with a process that asks you to create or select a secret to use. This list shows Secret Manager secrets and currently you probably don't have any available to use. Click Create to create a new one.
NOTE: Read the warning carefully as it tells you that if you name a secret with a
greengrass-prefix in its name then it is automatically granted access to be used by all AWS IoT Greengrass services.
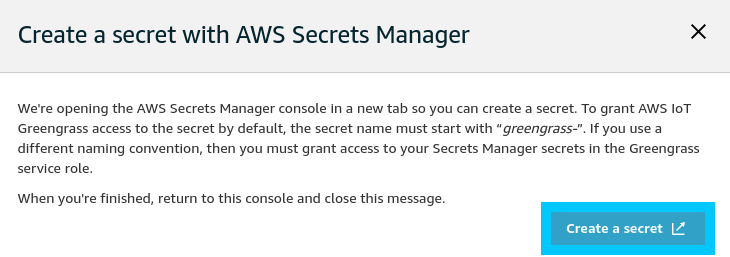
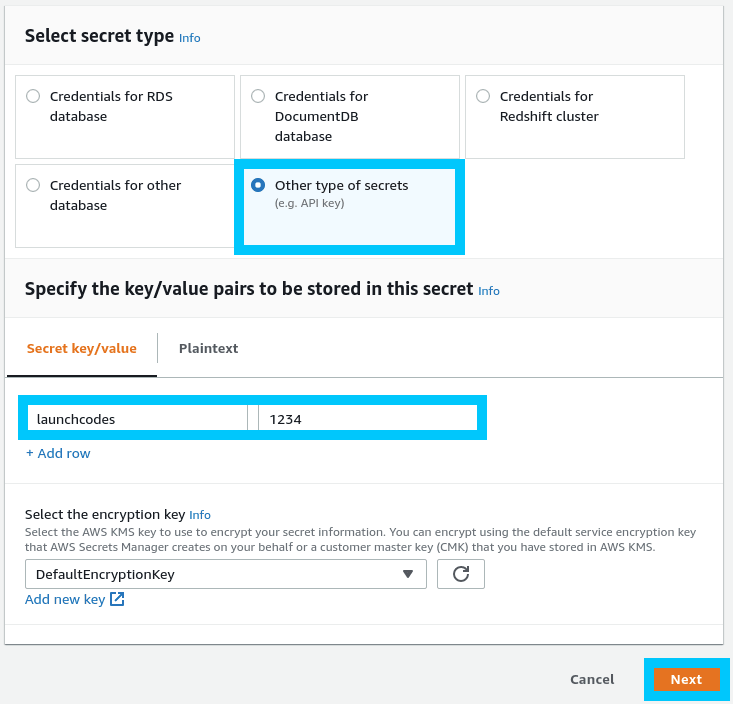
You will be pushed to the AWS Secrets Manager console where you will need to create a new secret. Go ahead and create something creative, just make sure you've selected Other type of secrets as the secret type. Click Next when you're ready to proceed.
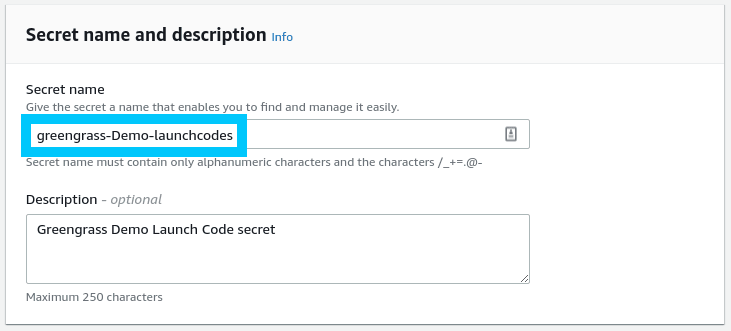
Give your secret a name, making sure that it is prefixed by greengrass-. In my case I've gone with greengrass-Demo-launchcodes but you can be as creative as you want. Click Next when you are ready to move on.
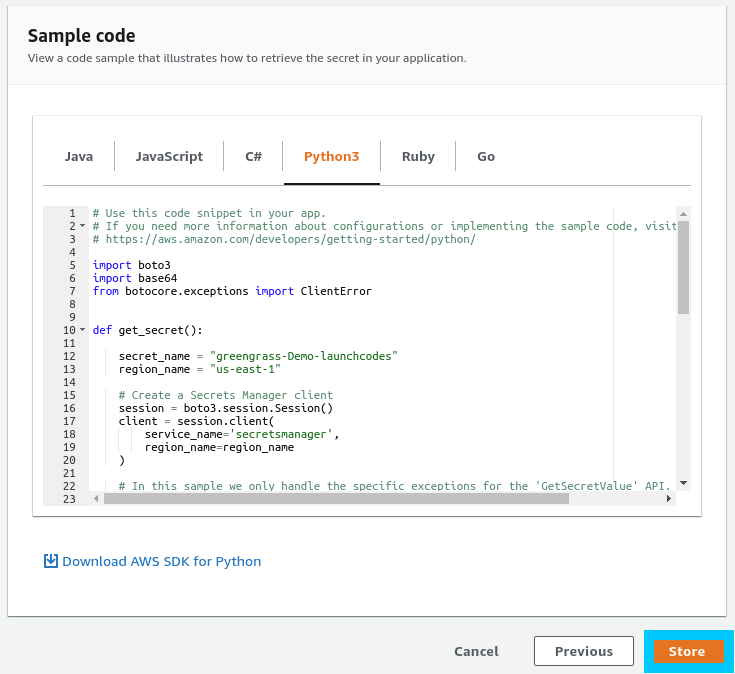
Click Next on the next screen as well (Configuring automatic rotation). The final screen gives you an overview of the secret we're creating, along with some useful client code to accessing the secret. Click Store to finalize the creation.
Now that the secret has been created navigate back to the AWS IoT Greengrass group tab and click Refresh on the secret selection page.
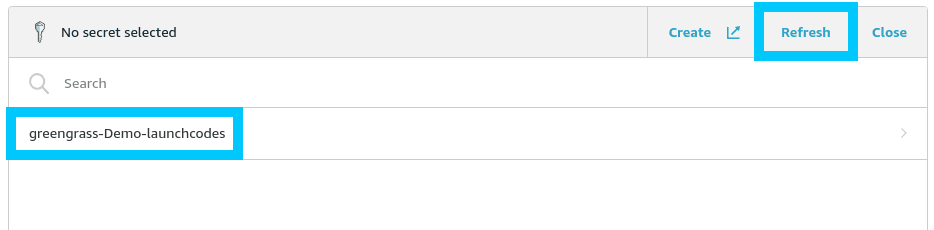
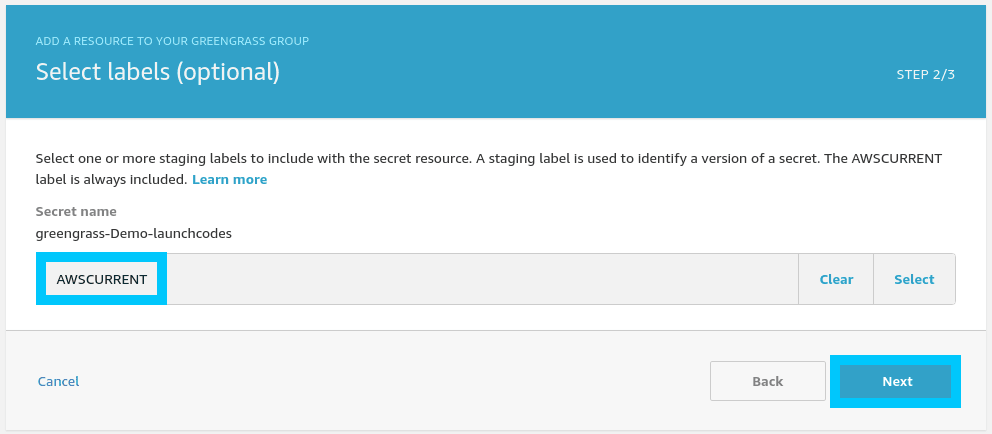
Click on the secret we just created (greengrass-Demo-launchcodes) then click Next on the Select labels page.
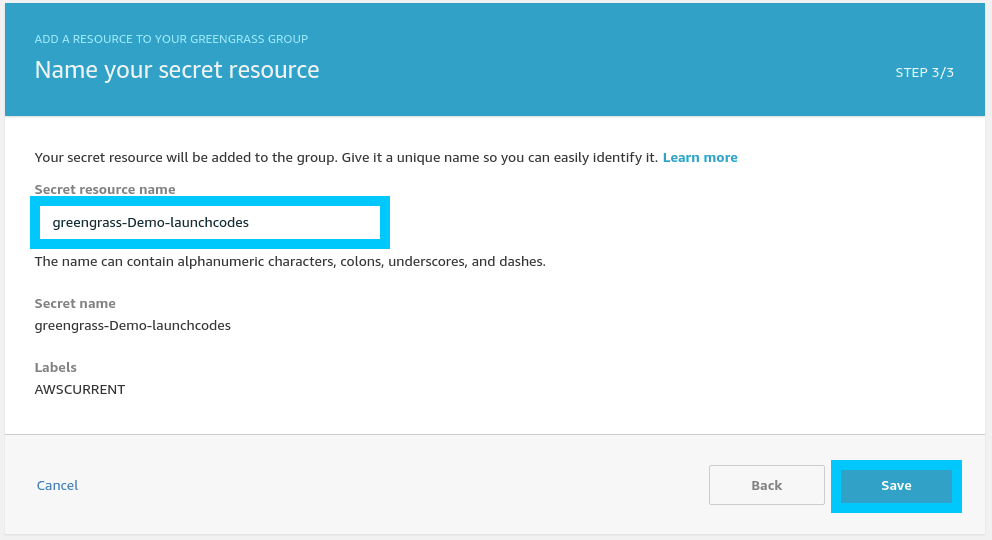
Finally give the Greengrass Secret a name and click Save to finalize its creation.
Greengrass Lambda function - Access Secrets
To create a new Lambda function for Greengrass we first need to grab a copy of the Greengrass SDK. For this tutorial we'll be using the Python SDK which can be downloaded from the github repo page.
Download and unzip the SDK to your computer; the following commands can be used if you're on MacOS or Linux.
# Download the Greengrass SDK
wget -O greengrass.zip https://github.com/aws/aws-greengrass-core-sdk-python/archive/v1.5.0.zip
# Unzip the SDK
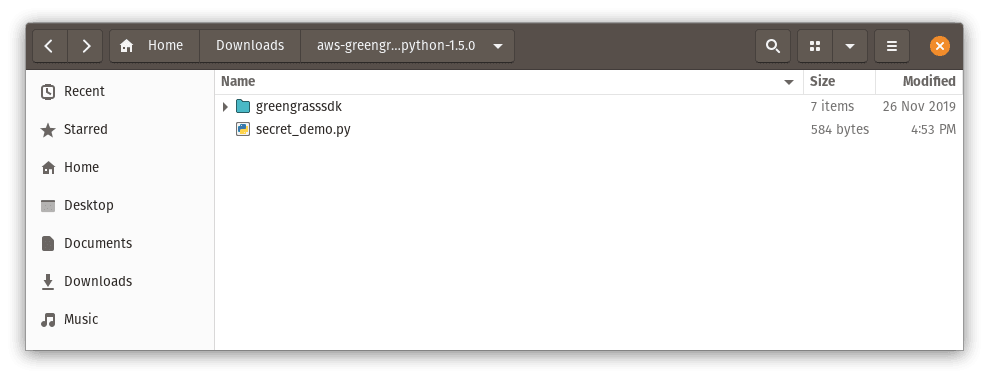
unzip -q greengrass.zipYou will be left with a directory called aws-greengrass-core-sdk-python-1.5.0 which has a couple subfolders. The important one is greengrasssdk. In fact delete all the folders except for greengrasssdk!
Then create a file called secret_demo.py next to the SDK folder.
Inside the secret_demo.py file add the following code for retrieving secret data
import greengrasssdk
secrets_client = greengrasssdk.client('secretsmanager')
message_client = greengrasssdk.client('iot-data')
iot_message = ''
def function_handler(event, context):
# SecretId should match your secret name
response = secrets_client.get_secret_value(SecretId='greengrass-Demo-launchcodes')
secret_value = response.get('SecretString')
if secret_value is None:
iot_message = '[FAILED] Retrieve secret.'
else:
iot_message = '[Success] Retrieved secret.'
# topic can be any topic name that you want to publish to
message_client.publish(topic='iot-demo-pub/secrets', payload=iot_message)
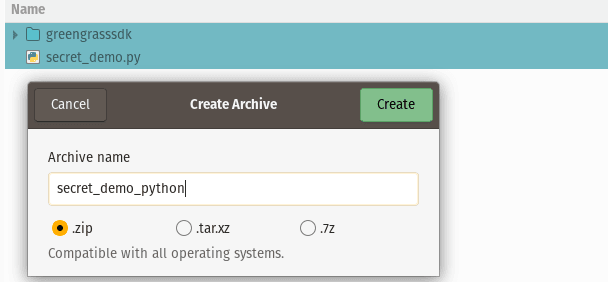
print('published: ' + iot_message)Now zip the greengrasssdk folder and secret_demo.py files up (not the root folder) into a zip file named whatever you like.
Head on back to the AWS IoT Greengrass console under your existing Greengrass group and select Add your first Lambda under Lambdas.
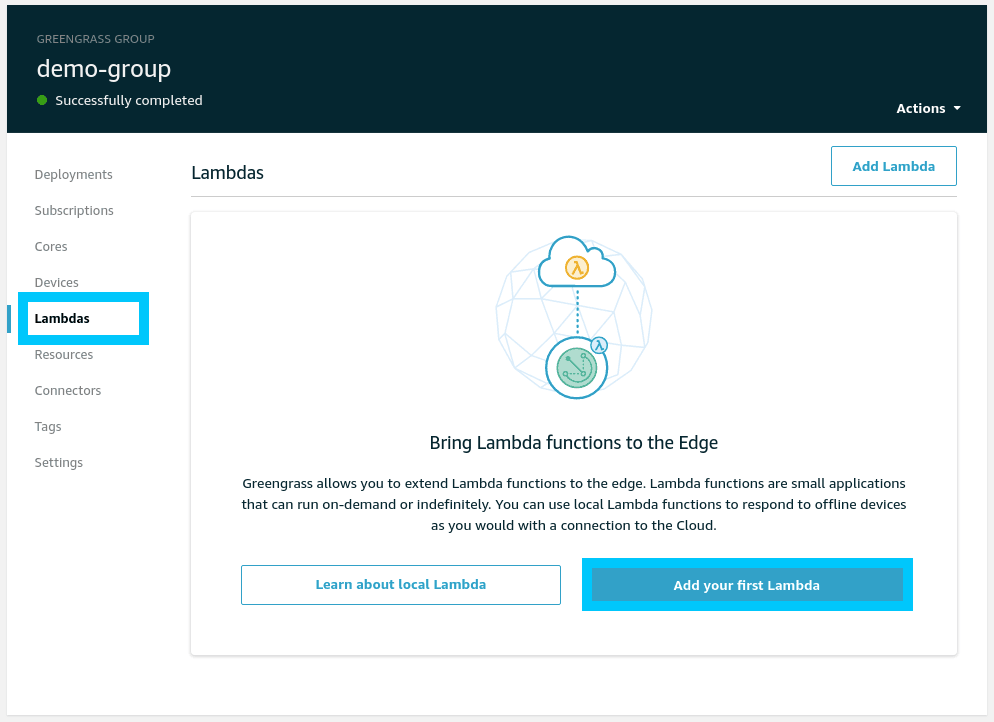
Click Create new Lambda when prompted which will open up a new Lambda console.
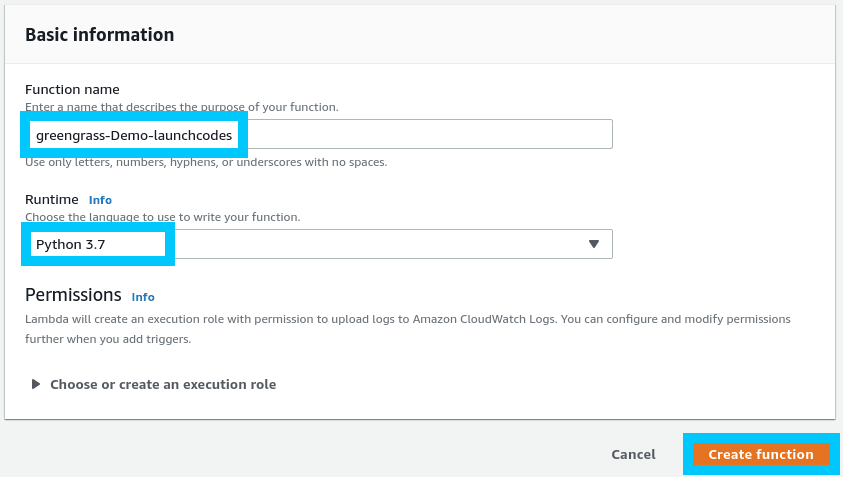
In the Lambda console Author from scratch a new function and use the Python 3.7 runtime. I've also named the lambda the same thing as our secret just to make things consistent. Click Create function when ready.
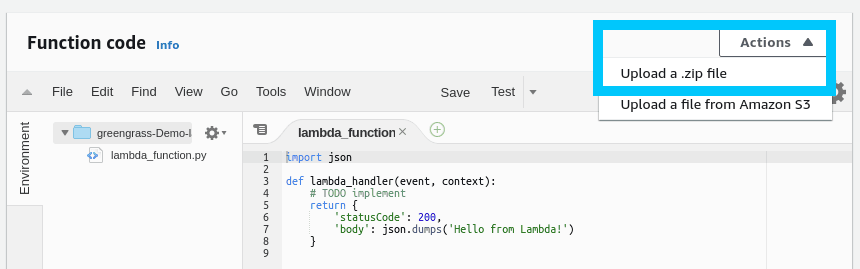
Scroll down to the Function code section and select Upload a .zip file from the Actions drop down.
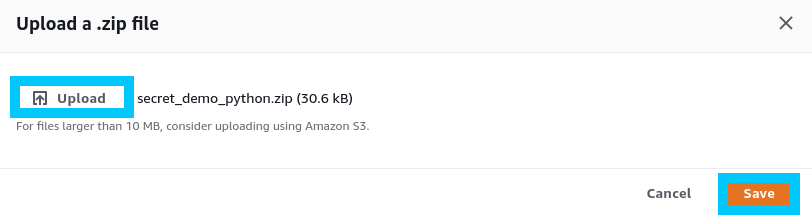
Select the zip file we created in the previous step and click Save.
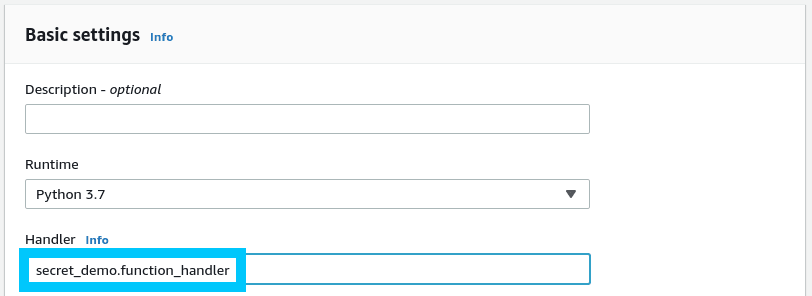
Scroll down to Basic settings for the lambda and edit the Handler to match the python file and function we created as well. In this case it is secret_demo.function_handler.
Click Save once the changes have been made.
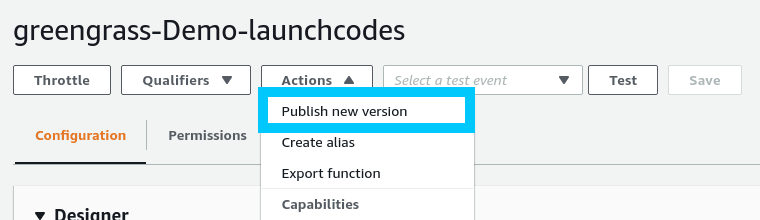
Finally head to the top of the Lambda function and select Actions > Publish new version. Click Publish in the follow up prompt.
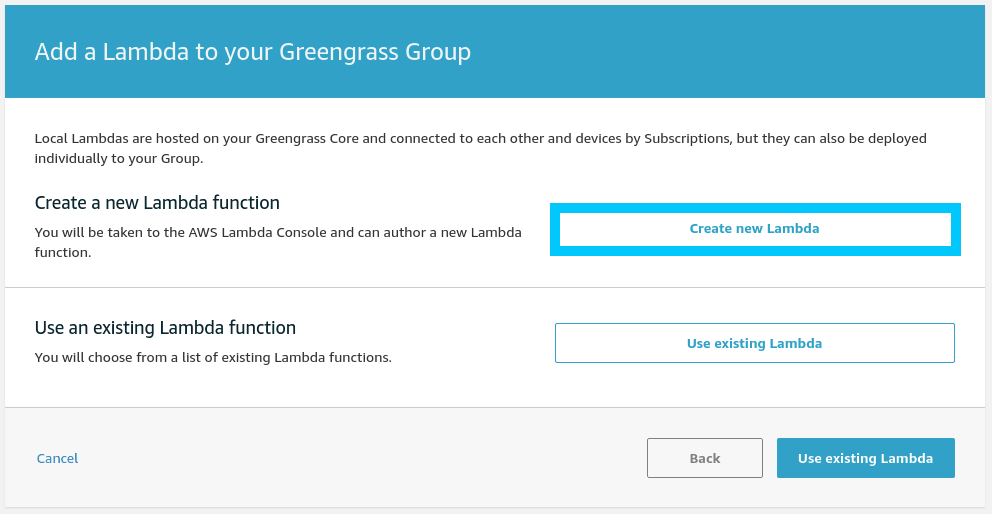
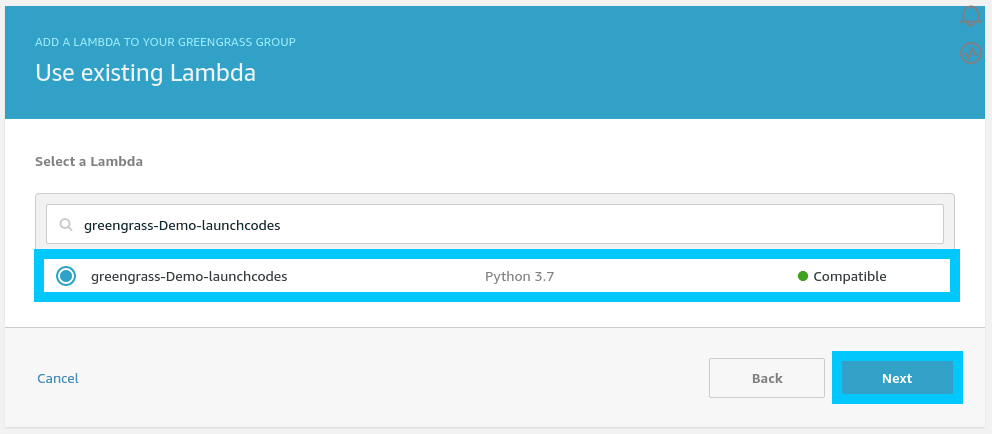
Navigate back to the AWS IoT Greengrass console and proceed to Use an existing Lambda function and select the one we just created. Click Next
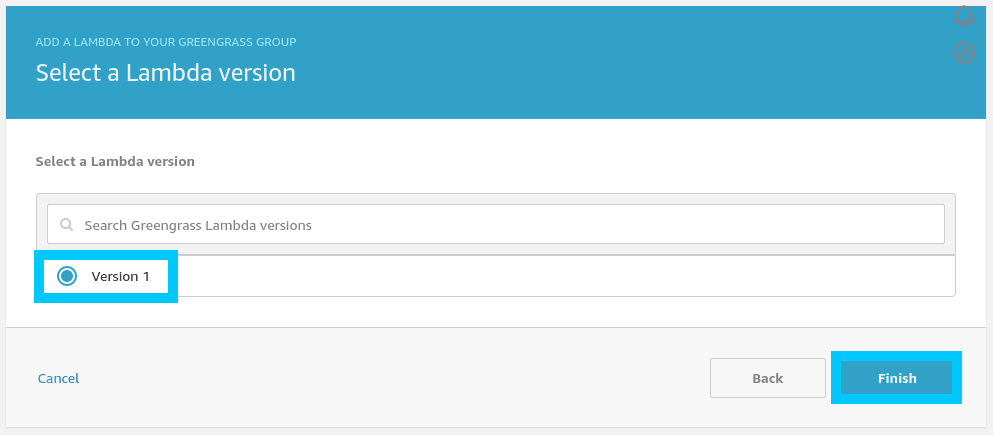
When prompted for your lambda version, select Version 1 (or whatever the most recent version for you is).
Create Subscriptions
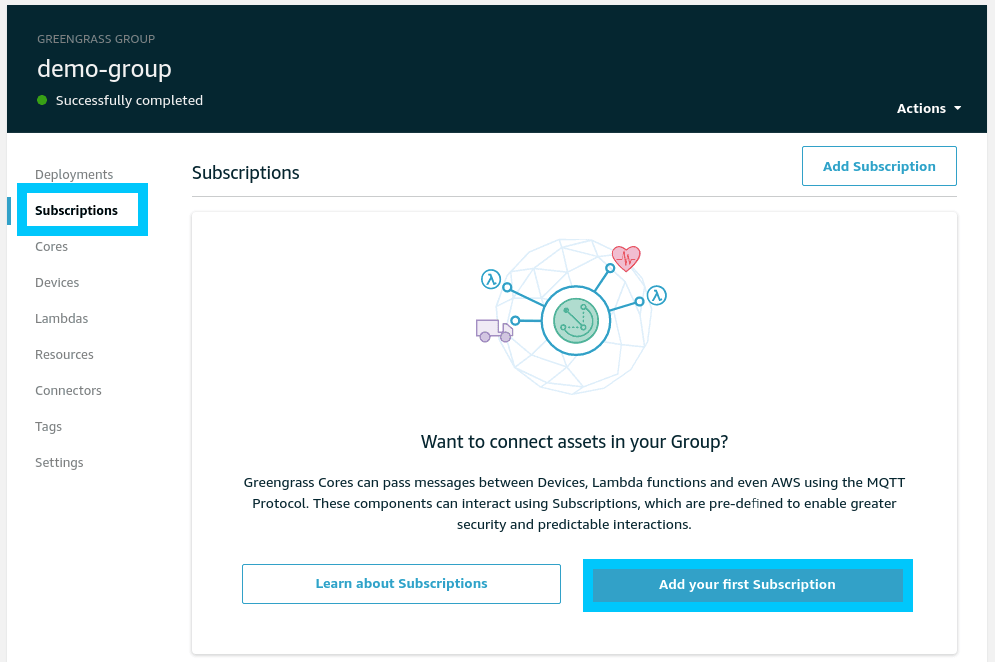
In order for the Lambda function and AWS IoT to communicate we also need to create a subscription for the Greengrass group. To do this navigate to the Subscriptions menu and select Add your first Subscription.
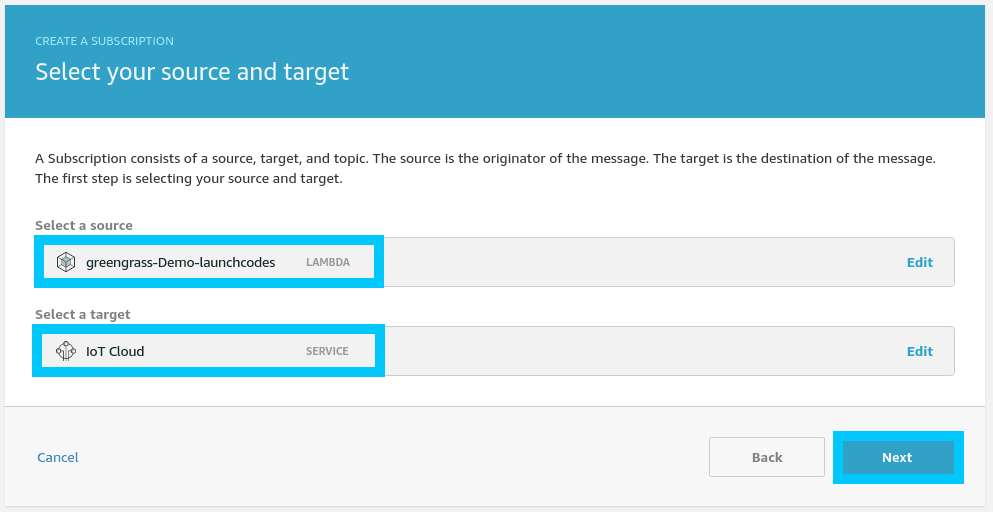
When asked for the source and target select:
- Source: Lambda (greengrass-Demo-launchcodes)
- Target: Service (IoT Cloud)
Click Next to move on.
When prompted for the topic filter, use whatever topic you used in the python source code. In my case I used iot-demo-pub/secrets.
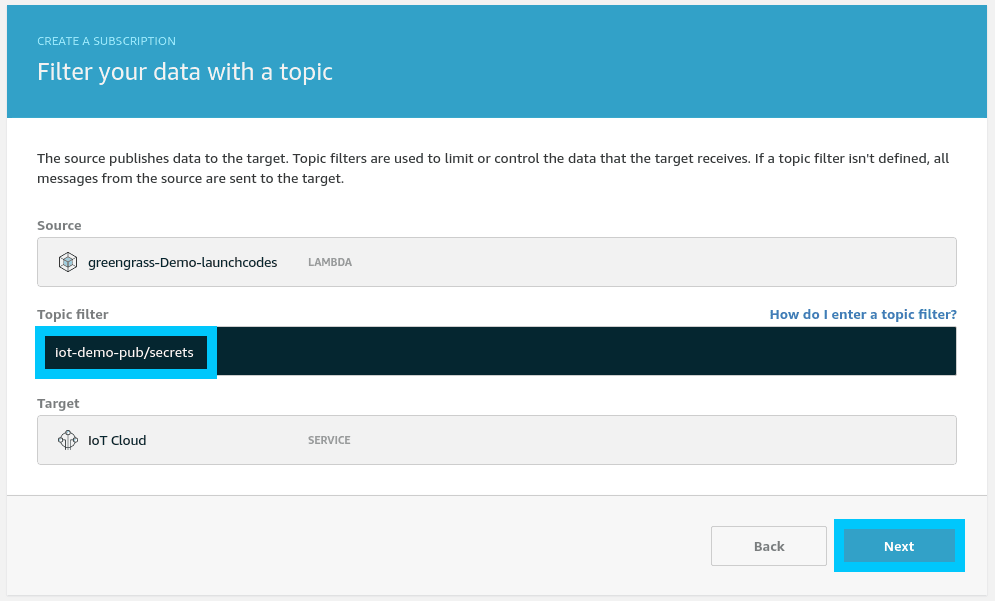
Click Next then Finish.
We will also need to create a second subscription that will be used to trigger the Lambda. To do this, repeat the steps above but instead this time select:
- Source: Service (IoT Cloud)
- Topic: iot-demo-pub/trigger
- Target: Lambda (greengrass-Demo-launchcodes)
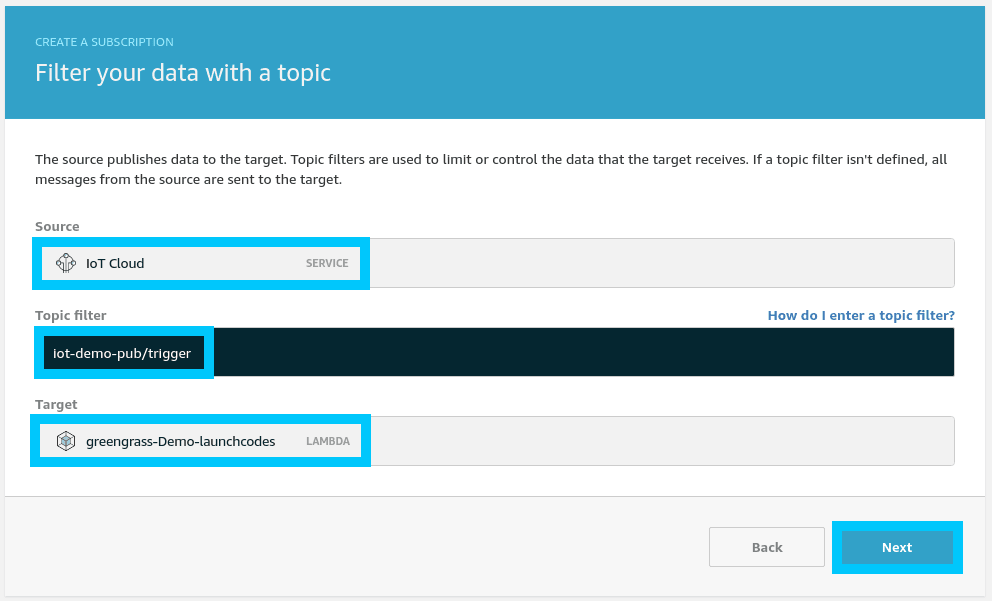
Click Next then Finish.
Deploy and Test Secret Access
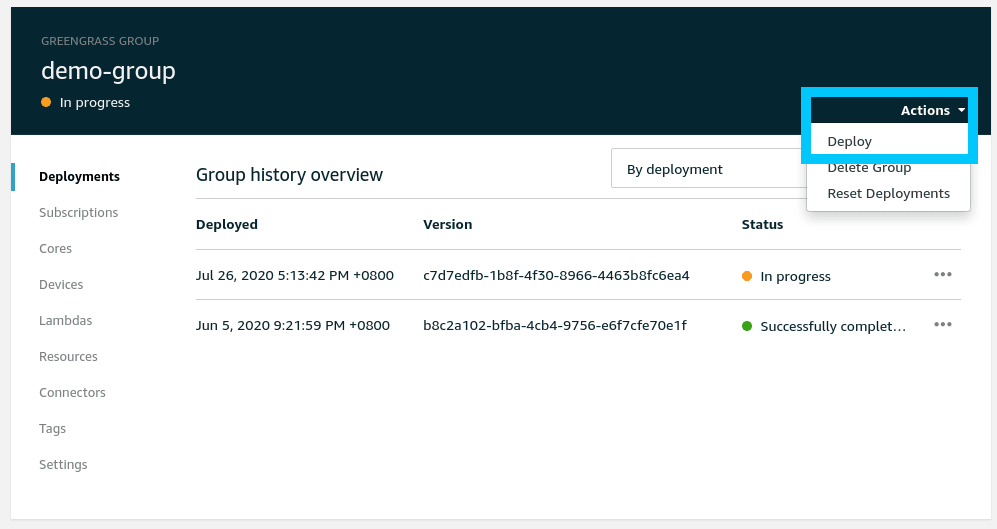
The final step for this tutorial is to deploy and test the secret we just created. On the Greengrass group select Actions > Deploy to push the Secret and Lambda out to the edge.
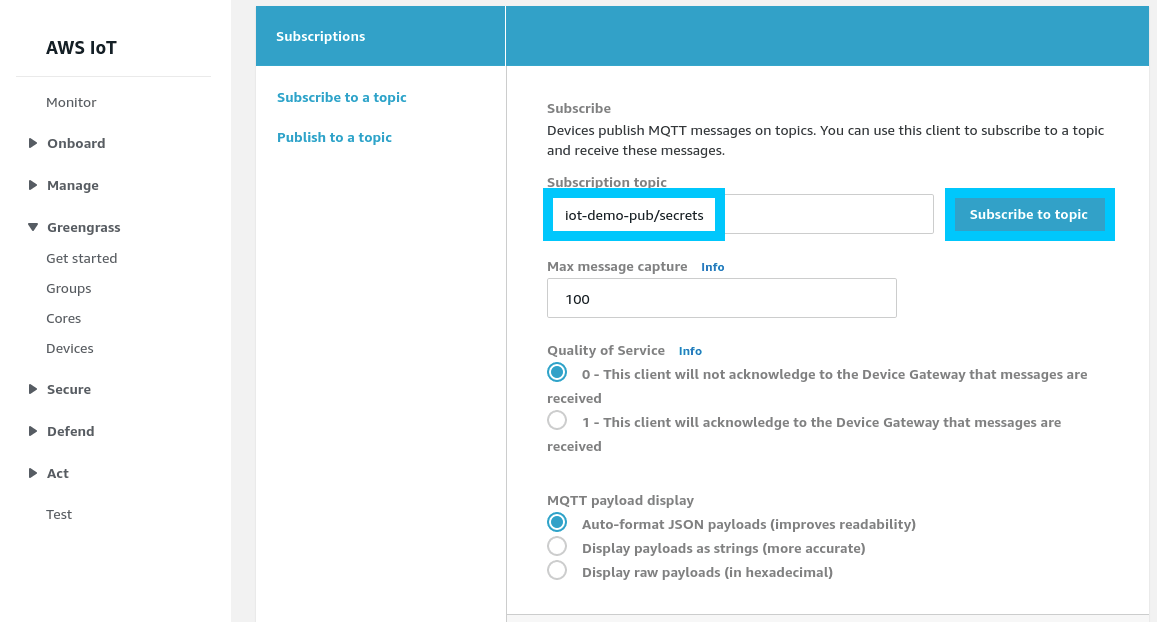
Once the deployment shows up as successful, navigate to the Test menu in AWS IoT Core. Input iot-demo-pub/secrets as the topic you want to subscribe to and click Subscribe to topic.
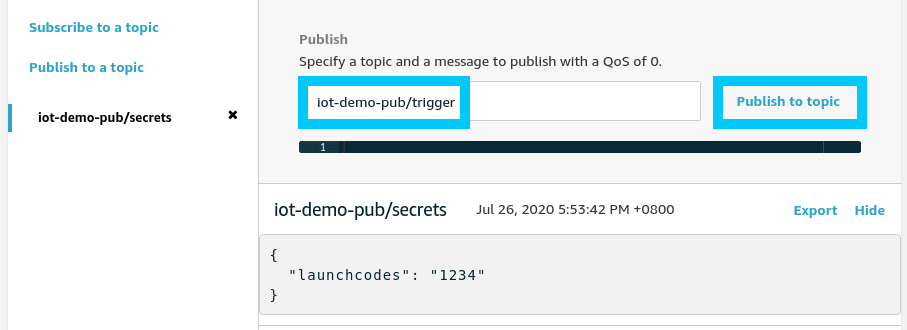
Then simply publish any message you want to iot-demo-pub/trigger to tell the edge lambda to fire. You should receive back the launch codes from secrets manager.
Summary
Congratulations! You created a Secret for the use at the edge in AWS IoT Greengrass Core. Now you can safely use secrets at the edge!
If you had any issues setting things up, or you have other questions, please let me know by reaching out on Twitter @nathangloverAUS or dropping a comment below.
